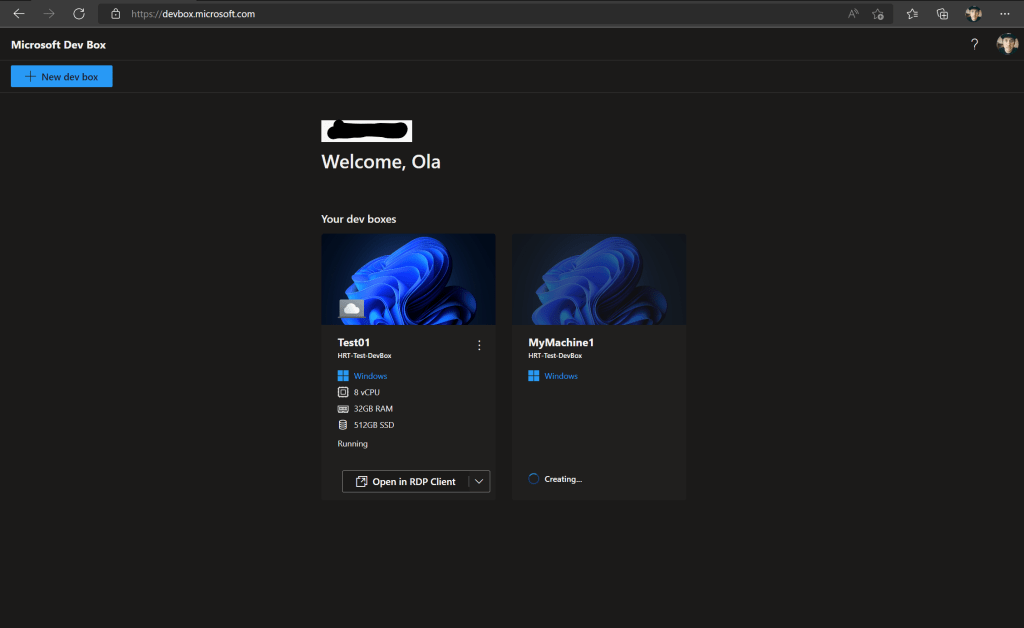
Some of you might have noticed that when updating a Windows 365 Cloud PC to Windows 11 24H2, the shutdown button appears out of nowhere in the start menu, which can cause some weird behavior for the end-users.

Shutting down the Cloud PC isn’t really anything you should be bothered with. Restarting, yes, but if you do a shutdown, it will boot back up again within a few minutes.
With the Windows 11 24H2 update to Windows 365, if you upgrade from an earlier Windows 11 version, this registry value will be reset.

While I still encourage you to provide feedback to Microsoft, the fix for this problem is fairly simple!
There are two ways we could go about addressing this. We could either create a configuration using the Settings Catalog or use proactive remediation. We will get the same result in the end, so it depends on how you like to do it. I will show you both ways in this blog post, and how you can configure it.
Settings catalog
In Microsoft Intune, head into Devices > Windows > Configuration and create a new configuration profile by clicking “+ Create“. Select Settings catalog as the profile type and click create.

Give the profile a good name which makes sense in your environment.

Search for “Start” and find “Hide Shutdown” in the list, then check the checkbox next to it. Close the fly-out.

Make sure to enable the setting before moving to the next step.

In my case, I will skip scope tags and move straight to Assignments, where I select “All devices” and filter out Windows 365 with a filter.

Last step is to review and create the policy. And then you just need to wait for the policy to apply.
Proactive remediation
The scripts
The easiest way to deploy a scripted solution for this is to use remediation, since then we can also get feedback on how many devices had this issue. We can have it continuously checking or just run once.
But in order to set up a remediation, we need a detection and a remediation script (you could run everything in the detection script, but you won’t get any feedback if you want to run it more than once).
You can find the scripts either on my GitHub repository or just copy them from here.
Detection script
# Created by Ola Ström, olastrom.com
# Date: 2025-01-21
# Version: 1.0
# PowerShell script to update the registry value
# Define the registry path and value
$registryPath = "HKLM:\SOFTWARE\Microsoft\PolicyManager\default\Start\HideShutDown"
$valueName = "value"
# Check the current value
$currentValue = (Get-ItemProperty -Path $registryPath -Name $valueName).$valueName
# Check the value and set the appropriate exit code
if ($currentValue -eq 1) {
Write-Output "Registry value is set to 1."
exit 0
} else {
Write-Output "Registry value is not set to 1."
exit 1
}Remediation script
# Created by Ola Ström, olastrom.com
# Date: 2025-01-21
# Version: 1.0
# PowerShell script to update the registry value
$registryPath = "HKLM:\SOFTWARE\Microsoft\PolicyManager\default\Start\HideShutDown"
$registryName = "value"
$registryValue = 1
# Set the registry value
Set-ItemProperty -Path $registryPath -Name $registryName -Value $registryValue
Write-Output "Registry value updated successfully."Intune part
In Microsoft Intune, navigate to Devices > Scirpts and remediations.

Select “+ Create” in the ribbon and give your remedation a good name, then press next.

Now we will add the detection and remediation scripts, which you need to save as PowerShell scripts on your device to upload to Microsoft Intune. Change the “Run script in 64-bit PowerShell” to yes, but leave all the other options at their default values and press next.

On the Assignment tab, select your target group. I’m using “All devices” with a filter for Windows 365.

On this step, you also set the schedule by pressing on the text “Daily”, which is the default value. You can then choose if you want it to run once, hourly, or daily.

When you have selected your schedule, press next to review your settings before pressing create.

And now we wait until the remedation runs…
Monitoring the remediation
You can follow up the progress of your remediation by checking the device status on the remediation you just created.

In this view, you can follow up on individual devices and see how many devices were affected.
If the script detects that the value is set to anything other than “1”, it will run the script to fix it, and you can see here if the issue was fixed or not. This is not dependent on whether the script runs on a schedule or just once; you will still get feedback if any issues were found.
What happens on the Cloud PC?
Both ways will give the same end result for the end-user: the shutdown button will disappear, removing the option to shut down the Cloud PC (which is good).

Take aways
I’m not saying that one way or the other is the correct way; it’s just different ways to address the problem. Both of them have advantages, where the settings catalog will set the value and always keep it that way, and the remediation will check if the value is incorrect and change it if needed.
You can also reuse this script for other registry entries you would like to change, so feel free to reuse it!